Source:
http://www.atelierweb.com/rcomm/index.htmPersonal Notes: I love this tool...one of the most comprehensive System Admin Tools ever. Uploading and downloading files, Mapping of ports with applications, live view of desktop with a fast refresh rate (uhmm almost fast)AWRC is a must-have for System Administrators and Helpdesk personnel. Recommended for a range of special remote access requirements, from Intelligence to Parental supervision. Runs across firewalls.Performs deep audits and all kinds of maintenance operations.Does not leave traces on remote.It is absolutely safe.
You may be familiar with utilities that allow remote management of computers.All those utilities require that you install software on the remote computer in order to process your requests and send the information back to you.The first thing that makes AWRC different is that it does not require that you install any kind of software on the remote machine. Sure, it seems impossible. We thought that also!
The second thing is that AWRC allows you to gather more information from the remote system than remote privileged users can dream about. By far and large, AWRC is the more powerful remote audit tool you can find.
The third thing is that AWRC provides a great set of tools for remote computer management. You can do virtually anything on the remote computer you do on the local system.
These are the main features and capabilities of Atelier Web Remote Commander, no other software provides this amount of functionality:
· Access to the remote computer desktop enabling the launch of software with the mouse or keyboard.
· Simulates all keystrokes on the remote keyboard computer.
· Wakes-up from screen-savers with a mouse-click or keystroke. Deals with password protected screen-savers.
· Simulates the security attention sequence (Ctrl+Alt+Del) on the remote to enable logon and on the default desktop. The default hotkey is Ctr+Alt+D.
· Provides access to disks, partitions, folders and files. The partitions or folders are not required to be open shares.
· Remote files can be downloaded or launched in the remote system. Files can be launched as another user (equivalent to RunAs).
· Local files can be uploaded to the remote system.
· Files can be remotely zipped or unzipped.
· New directories can be made and files and directories can be renamed.
· Remote files and directories can be deleted, copied or moved.
· Allows sending or receiving the Clipboard contents: text, pictures and other standard Windows Clipboard formats.
· Provides partition information, namely File System, Type, Serial Number, Volume Label, Capacity and Free space.
· Allows visualization of shares.
· Allows visualization of users list and account details as well as Local and Global groups.
· Allows instant retrieval of password hashes, for audit of strong password policy enforcement across the organization.
· Allows visualization and management of services. Services can be started, stopped, paused, resumed and even unloaded.
· Allows visualization of processes. Processes can be killed.
· Allows remote Shutdown, Power-Off and Reboot.
· System Information (Operating System, Processor, BIOS, Memory, Display Adapter and Logical printers).
· Complete and detailed Hardware Devices list.
· Physical memory viewer.
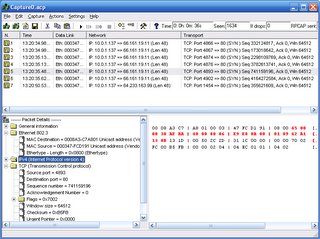
· Port Finder, which maps applications to open ports.
· Connections and Listening Ports, TCP statistics, UDP statistics, ICMP statistics, Routing Table, DNS Servers, Persistent Routes, IP Statistics/Settings, Installed Protocols/Protocol Details, Addressing Information Table, Net to Media Table, Interface Statistics/Settings.
· Chat facility for conversation with a remote interactive user.
· Provides antialiased scaling of remote desktop for comfortable viewing on the local computer.
· Uses Windows authentication, which guarantees that only individuals with Administrator privileges on the remote system are able to connect (strong passwords are obviously recommended).
· Can use strong encryption to keep the information out of reach from prying eyes.
· Request authorization feature for obtaining approval from remote before initiating operations.
· Transparent to Firewalls.
· Works within the company's Microsoft Networks LANs and across the Internet.
· Does not open any ports - it is absolutely transparent to any firewall, providing the Microsoft Networks operation is not blocked by the firewall.